You, the CEO of a small business, are under attack. Right now, extremely dangerous and well-funded cybercrime rings in China, Russia and the Ukraine are using sophisticated software systems to hack into thousands of small businesses like yours to steal credit cards, client information, and swindle money directly out of your bank account. Some are even being funded by their own government to attack American businesses.
In fact, the National Cyber Security Alliance reports that one in five small businesses have been victims of cybercrime in the last year – and that number is growing rapidly as more businesses utilize cloud computing, mobile devices and store more information online.
You can’t turn on the TV or read a newspaper without learning about the latest online data breach, and government fines and regulatory agencies are growing in number and severity. Because of all of this, it’s critical that you protect your business from these top 10 ways that hackers get into your systems.
#1. They Take Advantage Of Poorly Trained Employees
The #1 vulnerability for business networks are the employees using them. It’s extremely common for an employee to infect an entire network by opening and clicking a phishing e-mail (that’s an e-mail cleverly designed to look like a legitimate e-mail from a web site or vendor you trust). If they don’t know how to spot infected e-mails or online scams, they could compromise your entire network.
#2. They Exploit Device Usage Outside Of Company Business
You must maintain an Acceptable Use Policy that outlines how employees are permitted to use company-owned PCs, devices, software, Internet access and e-mail. We strongly recommend putting a policy in place that limits the web sites employees can access with work devices and Internet connectivity. Further, you have to enforce your policy with content-filtering software and firewalls.
We can easily set up permissions and rules that will regulate what web sites your employees access and what they do online during company hours and with company-owned devices, giving certain users more “freedom” than others.
Further, if the data in your organization is highly sensitive, such as patient records, credit card information, financial information and the like, you may not be legally permitted to allow employees to access it on devices that are not secured; but that doesn’t mean an employee might not innocently “take work home.” If it’s a company-owned device, you need to detail what an employee can or cannot do with that device, including “rooting” or “jailbreaking” the device to circumvent security mechanisms you put in place.
#3. They Take Advantage Of WEAK Password Policies
Passwords should be at least 8 characters and contain lowercase and uppercase letters, symbols and at least one number. On a cell phone, requiring a passcode to be entered will go a long way toward preventing a stolen device from being compromised. Again, this can be ENFORCED by your network administrator so employees don’t get lazy and choose easy-to-guess passwords, putting your organization at risk.
#4. They Attack Networks That Are Not Properly Patched With The Latest
Security Updates
New vulnerabilities are frequently found in common software programs you are using, such as Microsoft Office; therefore it’s critical you patch and update your systems frequently. If you’re under a managed IT plan, this can all be automated for you so you don’t have to worry about missing an important update.
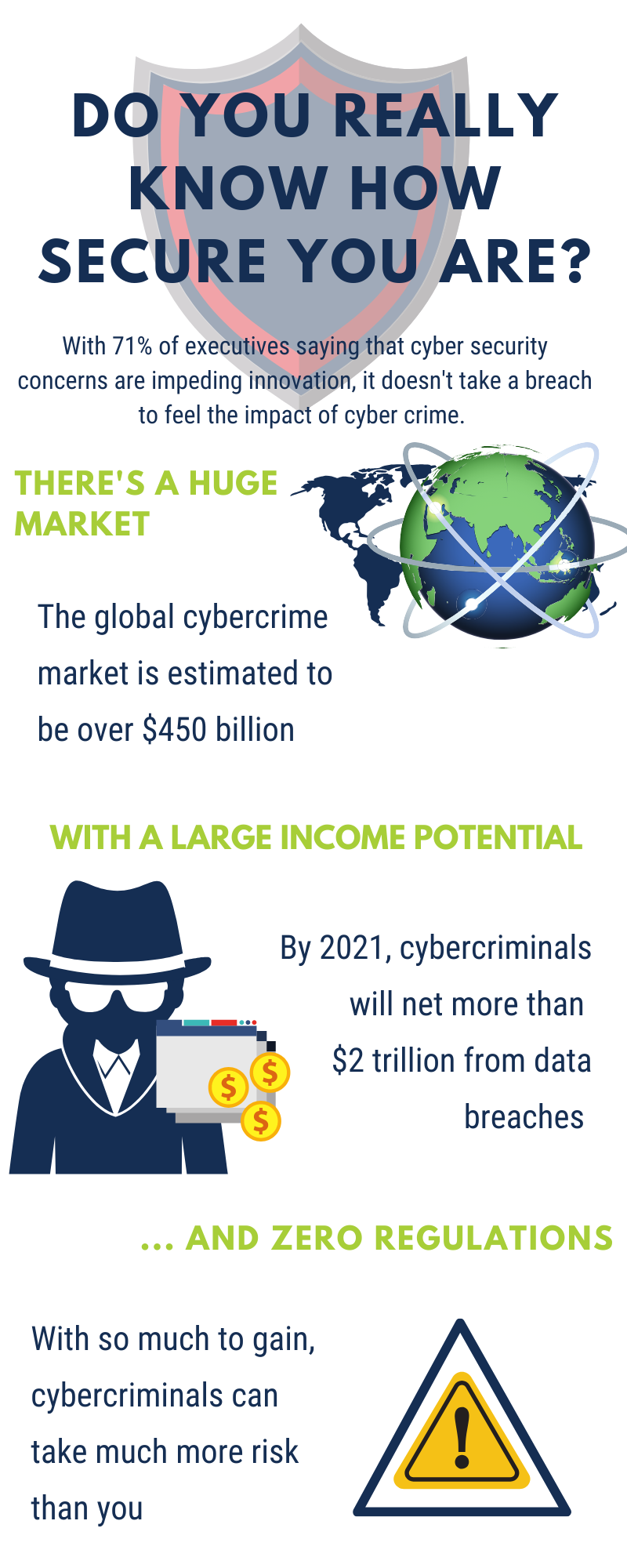
Want to learn more about cybersecurity? Learn about the latest cyber stories, statistics, and more below!
#5. They Attack Networks With No Backups Or Simple Single Location Backups

Simply having a solid, reliable backup can foil some of the most unauthorized access aggressive (and new) ransomware attacks, where a hacker locks up your files and holds them ransom until you pay a fee. If your files are backed up, you don’t have to pay a crook to get them back.
A good backup will also protect you against an employee accidentally (or intentionally!) deleting or overwriting files, natural disasters, fire, water damage, hardware failures and a host of other data-erasing disasters. Again, your backups should be AUTOMATED and monitored; the worst time to test your backup is when you desperately need it to work!
#6. They Exploit Networks With Employee Installed Software
One of the fastest ways cybercriminals access networks is by duping unsuspecting users to willfully download malicious software by embedding it within downloadable files, games or other “innocent”-looking apps. This can largely be prevented with a good firewall and employee training and monitoring.
#7. They Attack Inadequate Firewalls.
A firewall acts as the frontline defense against hackers blocking everything you haven’t specifically allowed to enter (or leave) your computer network. But all firewalls need monitoring and maintenance, just like all devices on your network. This too should be done by your IT person or company as part of their regular, routine maintenance.
#8. They Attack Your Devices When You’re Off The Office Network

It’s not uncommon for hackers to set up fake clones of public WiFi access points to try and get you to connect to THEIR WiFi over the legitimate, safe public one being made available to you. Before connecting, check with an employee of the store or location to verify the name of the WiFi they are providing.
Next, NEVER access financial, medical or other sensitive data while on public WiFi. Also, don’t shop online and enter your credit card information unless you’re absolutely certain the connection point you’re on is safe and secure.
Want to try the nations best frontline defense with Cisco? Get a FREE 14 day trial below!
#9. They Use Phishing E-mails To Fool You Into Thinking That You’re Visiting A Legitimate Web Site
A phishing e-mail is a bogus e-mail that is carefully designed to look like a legitimate request (or attached file) from a site you trust in an effort to get you to willingly give up your login information to a particular web site or to click and download a virus.
Often these e-mails look 100% legitimate and show up in the form of a PDF
(scanned document) or a UPS or FedEx tracking number, bank letter, Facebook
alert, bank notification, etc. That’s what makes these so dangerous – they LOOK
exactly like a legitimate e-mail.
#10. They Use Social Engineering And Pretend To Be You
This is a basic 21st -century tactic. Computer hackers pretend to be you to reset your passwords. In 2009, social engineers posed as Coca-Cola’s CEO, persuading an exec to open an e-mail with software that infiltrated the network. In another scenario, hackers pretended to be a popular online blogger and got Apple to reset the author’s iCloud password.